
From checking to weighing: what makes BIO 2 different from BIO 1






With this review, the BIO has grown into the basic standards framework for information security within the government. BIO 2 is more in line with international security standards, raises the bar for various security measures and is explicitly tailored to the requirements of the NIS2 directive. In addition, BIO 2 is part of the obligations of the Cybersecurity Act (Cbw), which means that the standards framework not only provides direction, but also increasingly gives legal importance.
The introduction of BIO 2 marks an important change in how the Dutch government deals with information security. Where BIO 1 was mainly about complying with prescribed measures, BIO 2 emphasizes risk-based work, personal responsibility and proven effectiveness.
Much has already been written about this change. But those who work with government organizations on a daily basis will see that the practice is more stubborn than the theory. In this article, we therefore compare BIO 1 and BIO 2, look at the practical implementation of BIO 2 and zoom deeper into the subject of passwords.
BIO 1 and BIO 2 in a nutshell: what has changed?
BIO 1: clear, but mainly focused on compliance
BIO 1 was highly compliance-driven. The standards framework worked with predefined measures that were largely conceived centrally. In many cases, organizations did not have to think about their risks themselves, but had to demonstrate that they had implemented certain measures.
That had advantages. BIO 1 was relatively easy to follow and made sure that topics such as password usage and authentication were even on the agenda. At the same time, this approach often led to ticking off in practice, says Rick Swinkels, Commercial lead (CCO) at MindYourPass. Measures were implemented “because they had to”, not because it was clear what risk they covered. Organizations, for example, purchased a password manager, but hardly stopped to consider whether it was actually being used, whether it really reduced the risk and how it could be measured.
BIO 2: risk-driven, context-dependent and legally heavier
BIO 2 explicitly breaks with this approach. The core of the new BIO is that risk analysis is leading. Organizations must gain insight into their biggest risks themselves, choose appropriate measures and then demonstrate that those measures are effective. This is in line with international standards such as ISO 27001.
In addition, BIO 2 has a stronger legal basis, including through the link with NIS2 and the Cyber Resilience Act. Where in practice, BIO 1 had few consequences for non-compliance, BIO 2 gets more weight through enforcement and administrative responsibility.
In theory, this is a more mature approach. In practice, it also requires considerably more knowledge, discipline and measurability. Security only has value if measures are based on actual insight into risks, says Rick. “It's not about taking a measure, but whether you can show what risk it reduces and whether that effect is also visible,” he says. In this sense, he believes that risk-based working is a necessary step forward compared to ticking off pre-established measures.
After all, a good risk analysis is not an exercise. It requires full insight into processes, data, dependencies and threats. It requires up-to-date knowledge of attack techniques, coordination between IT, security and governance, and an explicit discussion about risk tolerance. Moreover, risk assessments are rarely fully objective: they are influenced by experience, level of knowledge and administrative pressure. Without mature governance, risk-based work can therefore shift unnoticed from data-driven to opinion-driven.
Merijn de Jonge, founder and CEO of MindYourPass, does make a critical comment. He points out that government organizations are essentially dealing with the same processes, data and threats, but within BIO 2 are still given the freedom to interpret risks and measures in their own way. “Then fragmentation will automatically occur,” he warns. “Some municipalities have strict standards, others have minimal standards, while for citizens, it's just one government.” According to Merijn, this inequality actually undermines the trust that BIO 2 should strengthen.
Nowhere does this tension between freedom and uniformity come out more sharply than with the subject of passwords.
Password policy from BIO 1 to BIO 2: what's changing?
Passwords under BIO 1: concrete, but quickly out of date
In BIO 1, password policy was developed relatively concretely. There were guidelines with technical details and explicit references to solutions such as a password vault. This was nice for many organizations: it was clear what was expected. But this concreteness also had disadvantages: the standard made technical choices and steered the market, guidelines became obsolete quickly and the focus was on having a tool, not on safe behavior or risk reduction.
In practice, this meant that organizations were able to comply with BIO 1 without improving actual password usage: ticking the box was sufficient.
Passwords under BIO 2: abstract where it should be concrete
BIO 2 emphatically opts for a higher level of abstraction. The standard requires that organizations must offer employees a password manager or similar solution and that password requirements must be enforced automatically.
What is missing is just as remarkable: it does not say what these requirements are, there is (for now) no standard for password quality, uniqueness or reuse, and there is no mention of how organizations should determine what is “good enough”.
According to Merijn, this is nothing short of problematic. According to him, password quality is not an issue for individual risk considerations, but basic hygiene. Leaving this completely open creates arbitrariness: one municipality has strict requirements, the other minimal ones, depending on level of knowledge, culture or available time.
Although Rick understands why BIO 2 does not lay down technical details - because standards must be future-proof - he also sees the same risk: without additional frameworks and support, organizations can formally comply but fall short in terms of content.
The practical problem: risk analysis without full insight
BIO 2 relies heavily on risk analyses. But in practice, it appears that many government organizations do not fully understand their application landscape. Shadow IT, external SaaS solutions and links out of the sight of IT departments are the rule rather than the exception. This creates a fundamental problem: a risk analysis based on incomplete information is by definition unreliable.
In addition, risk analyses are often carried out periodically and are largely based on interviews, policy documents and assumptions about the use of systems. In rapidly changing IT environments, these assumptions are rapidly aging. What is classified as “low risk” on paper may prove vulnerable in practice because applications are used differently than expected. A risk analysis is therefore not an objective fact, but the result of available information, interpretations and choices.
This is extra relevant when it comes to passwords. Without measurements, it remains invisible how many passwords are reused, which accounts pose the greatest risk, or where strong requirements exist in theory but are circumvented in practice. “Many risk analyses are defensible on paper, but lack factual substantiation,” says Merijn.
BIO 1 & BIO 2: A comparison
What does this mean for government organizations?
BIO 2 requires maturity. Not every organization has the same knowledge, capacity or resources to properly analyze risks and implement measures effectively. This leads to differences in security levels: exactly what BIO 2 tries to prevent.
On the positive side, BIO makes 2 responsibilities more explicit. Directors are ultimately responsible, and the CISO advises. Cybersecurity is thus moving from an IT topic to an administrative one. But without objective measures, it remains difficult to determine when something is “sufficient”.
MindYourPass's vision: measure first, choose later
BIO 2 is not a problem, but an invitation. An invitation to stop basing information security on assumptions and checklists, but on facts. Especially when it comes to passwords - still one of the most important attack vectors - risk-based working requires more than just good intentions.
In practice, this means: first gaining insight into the entire application landscape, then actually measuring how passwords are used, objectifying the risks and only then choosing and enforcing measures. Without that order, risk-based working remains a paper exercise. With measurements, it becomes a steering tool.
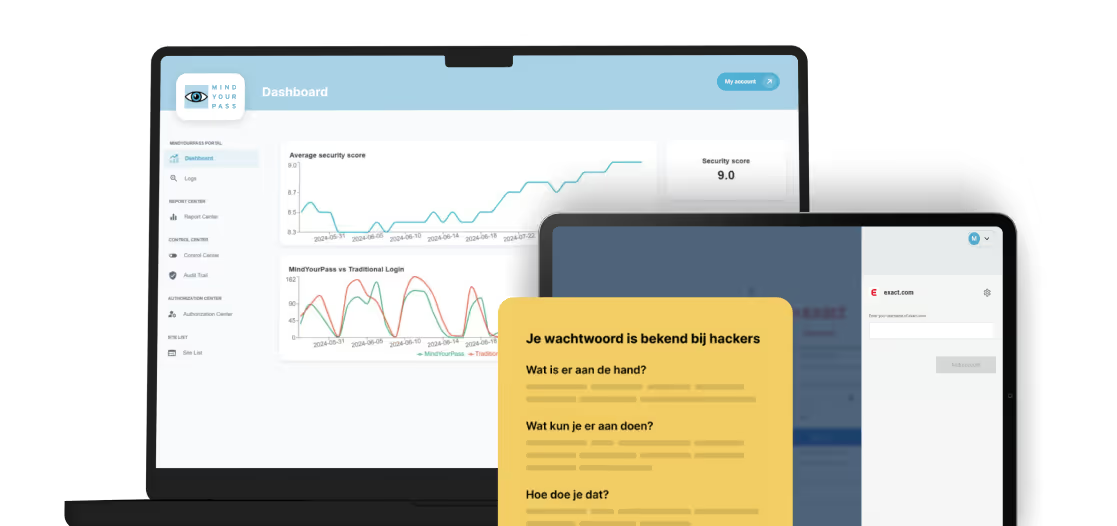
You can see that, for example, in the Kempen municipalities, where five municipalities and two common regulations work together on a single ICT environment. They were already using password solutions, but lacked insight and discipline: employees reused passwords or stored them locally. With MindYourPass, they got central control over five municipalities, enforceable password policies and dashboards that show where risks actually lie. Adoption is now around 80% and privacy officers and ICT administrators use the reports to make targeted adjustments.
In terms of content, BIO 2 is a clear step forward compared to BIO 1. It forces organizations to think, take responsibility and demonstrate the effectiveness of measures. At the same time, the standard deliberately leaves crucial topics, in particular passwords, open. That is precisely where the risk of non-commitment lies.
The real challenge for the government therefore lies not in fewer rules, but in better choices. Choices that are supported by measurable facts rather than assumptions. Only then will risk-based work not only become a new starting point, but also an actual risk reduction.
Get in touch with us.
Let MindYourPass make your organization safe.

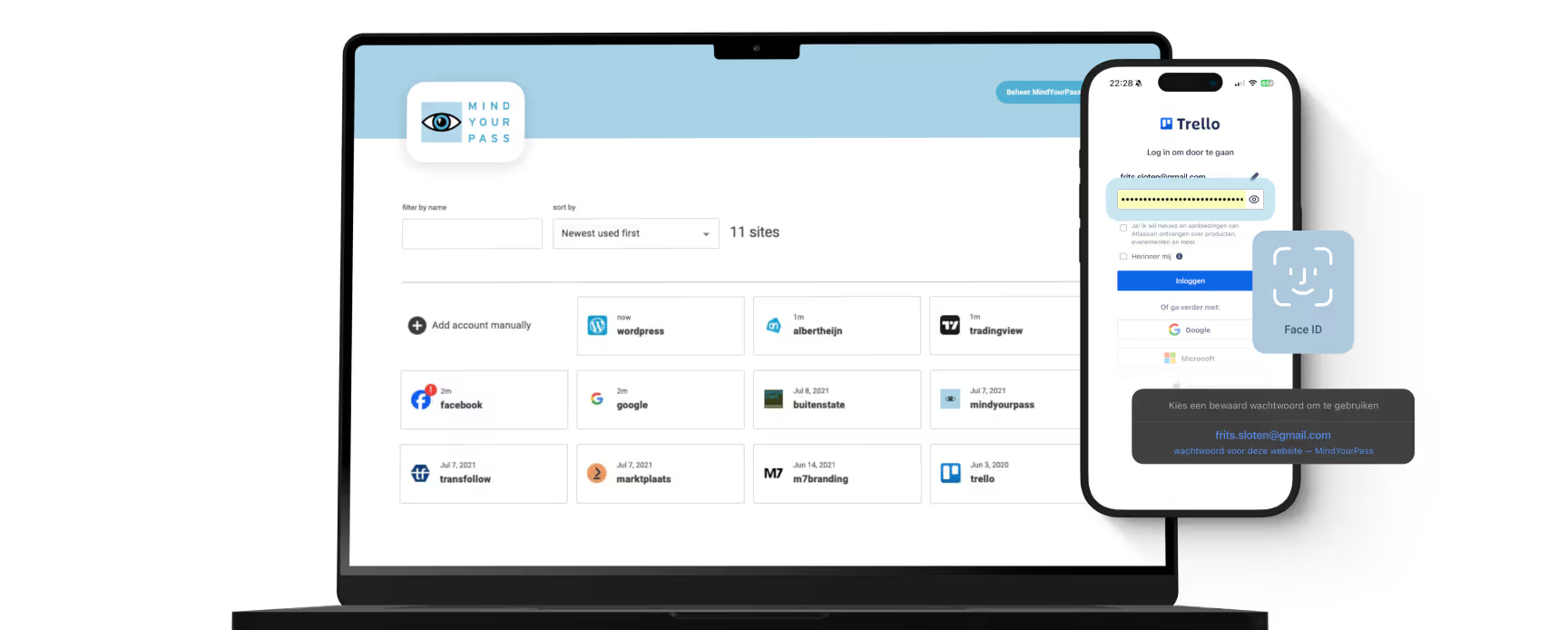
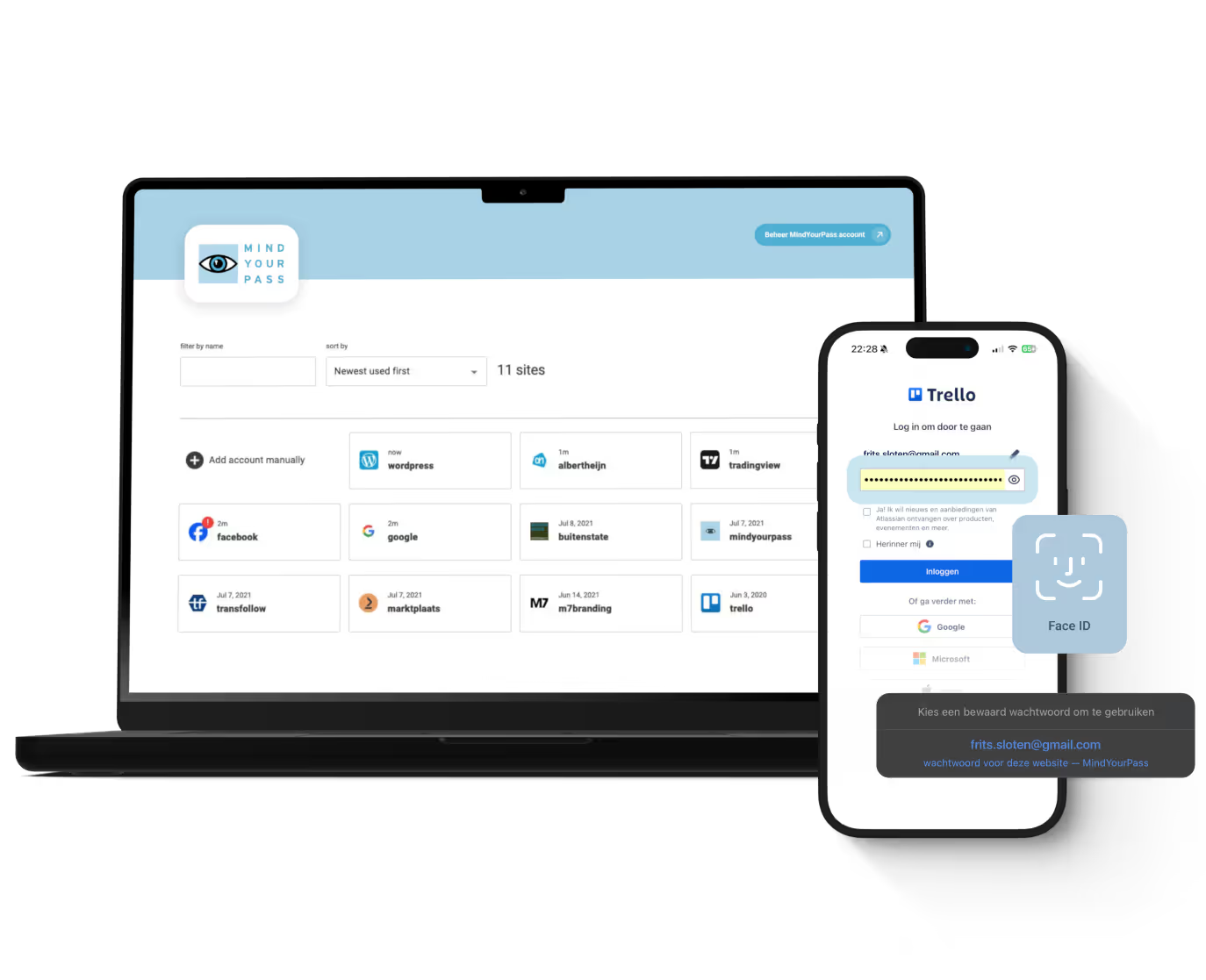
Log in securely with ease.
At home and at work.




Triple-i™ improvement method
De kluisloze wachtwoordmanager van MindYourPass
Met de wachtwoordmanager van MindYourPass maak je eenvoudig al je wachtwoorden ijzersterk en uniek. De wachtwoordmanager beheert jouw wachtwoorden, waarmee jij dagelijks kunt inloggen op al je accounts. Zonder dat jij je wachtwoorden hoeft in te typen. Dat doet MindYourPass voor je.










